Minimizing Information Disclosure To Third Parties in Social Login Platforms
Over the past few months we are seeing a large and ever increasing number of Web sites encouraging users to log in with their Facebook, Twitter, or Gmail identity, or personalize their browsing experience through a set of plug-ins that interact with the users' social profile. Research results suggest that more than two million Web sites have already adopted Facebook's social plug-ins, and the number is increasing sharply. Although one might theoretically refrain from such single sign-on platforms and cross-site interactions, usage statistics show that more than 250 million people might not fully realize the privacy implications of opting-in. To make matters worse, certain Web sites do not offer even the minimum of their functionality unless the users meet their demands for information and social interaction. At the same time, in a large number of cases, it is unclear why these sites require all that personal information for their purposes.
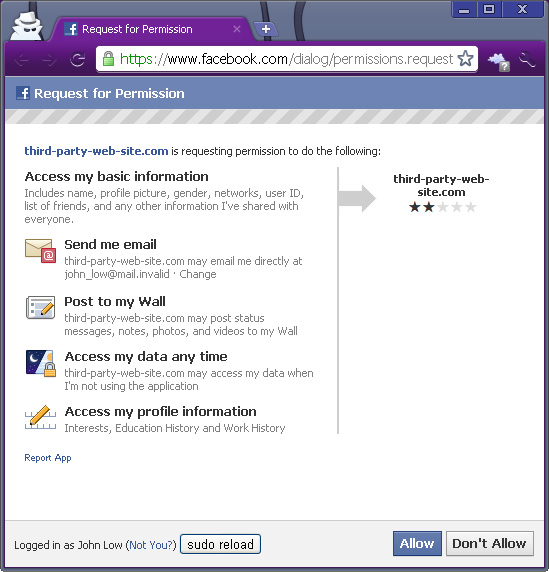
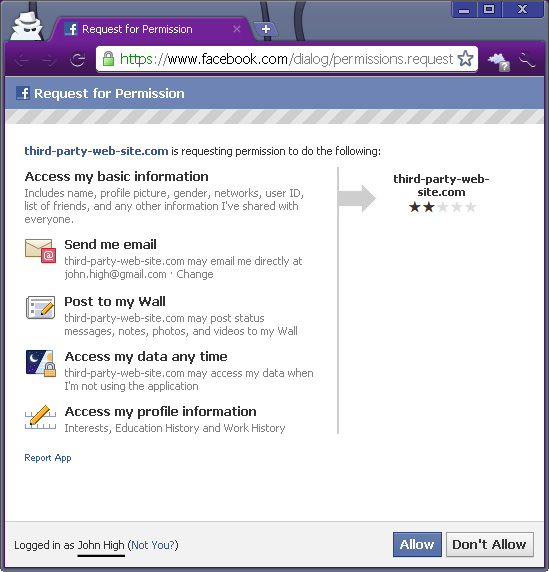
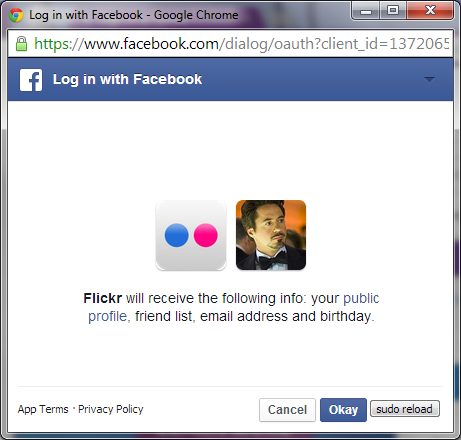
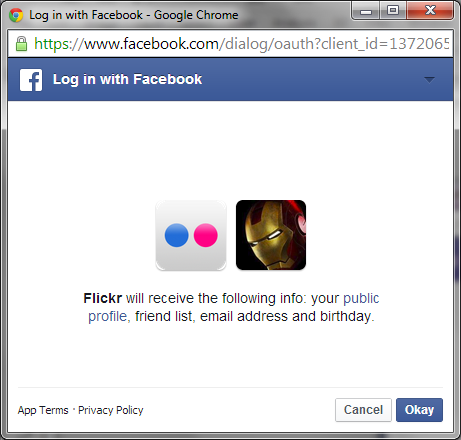
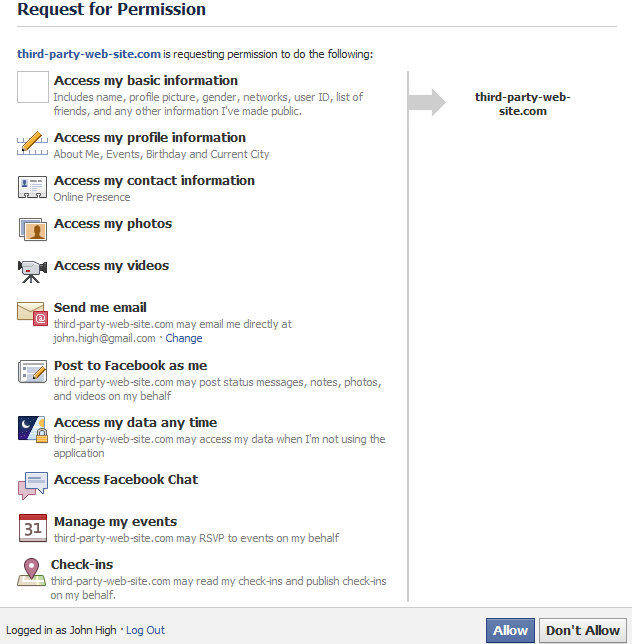
This research project aims at mitigating this problem by designing and developing a framework for minimum information disclosure across third-party sites with social login interactions. Our example case is Facebook, which combines a very popular single sign-on platform with information-rich social networking profiles. When a user wants to browse a Web site that requires authentication or social interaction with his Facebook identity, our system employs, by default, a Facebook session that reveals the minimum amount of information necessary. The user has the option to explicitly elevate that Facebook session in a manner that reveals more or all of the information tied to his social identity. This enables users to disclose the minimum possible amount of personal information during their browsing experience on third-party Web sites.
People
Georgios Kontaxis (E-Mail: kont...@cs.columbia.edu)
Michalis Polychronakis (E-Mail: mike...@cs.columbia.edu)
Evangelos P. Markatos (E-Mail: mark...@ics.forth.gr)
Refereed Publications
Minimizing Information Disclosure to Third Parties in Social Login Platforms. Georgios Kontaxis, Michalis Polychronakis, and Evangelos P. Markatos. International Journal of Information Security (IJIS), vol. 11, no. 5, pp. 321-332, 2012. DOI: 10.1007/s10207-012-0173-6
SudoWeb: Minimizing Information Disclosure to Third Parties in Single Sign-On Platforms. Georgios Kontaxis, Michalis Polychronakis, and Evangelos P. Markatos. In Proceedings of the 14th Information Security Conference (ISC). October 2011, Xi'an, China. (Best Student Paper Award) (Acceptance rate: 26%)
Software
We implement a prototype of our framework as a browser extension for the Google Chrome browser. Our prototype supports the popular single sign-on mechanism "Facebook Connect". We make our code (beta version) available here.